Day 156: Building Your Security Command Center - SIEM Implementation
What You’re Building Today
Imagine you’re the security operations lead at a financial services company processing millions of transactions. Your log processing system captures everything—user logins, API calls, database queries, network traffic. But buried in this tsunami of data are the signals that matter: the suspicious login from an impossible location, the subtle pattern of reconnaissance, the gradual privilege escalation that screams “breach in progress.”
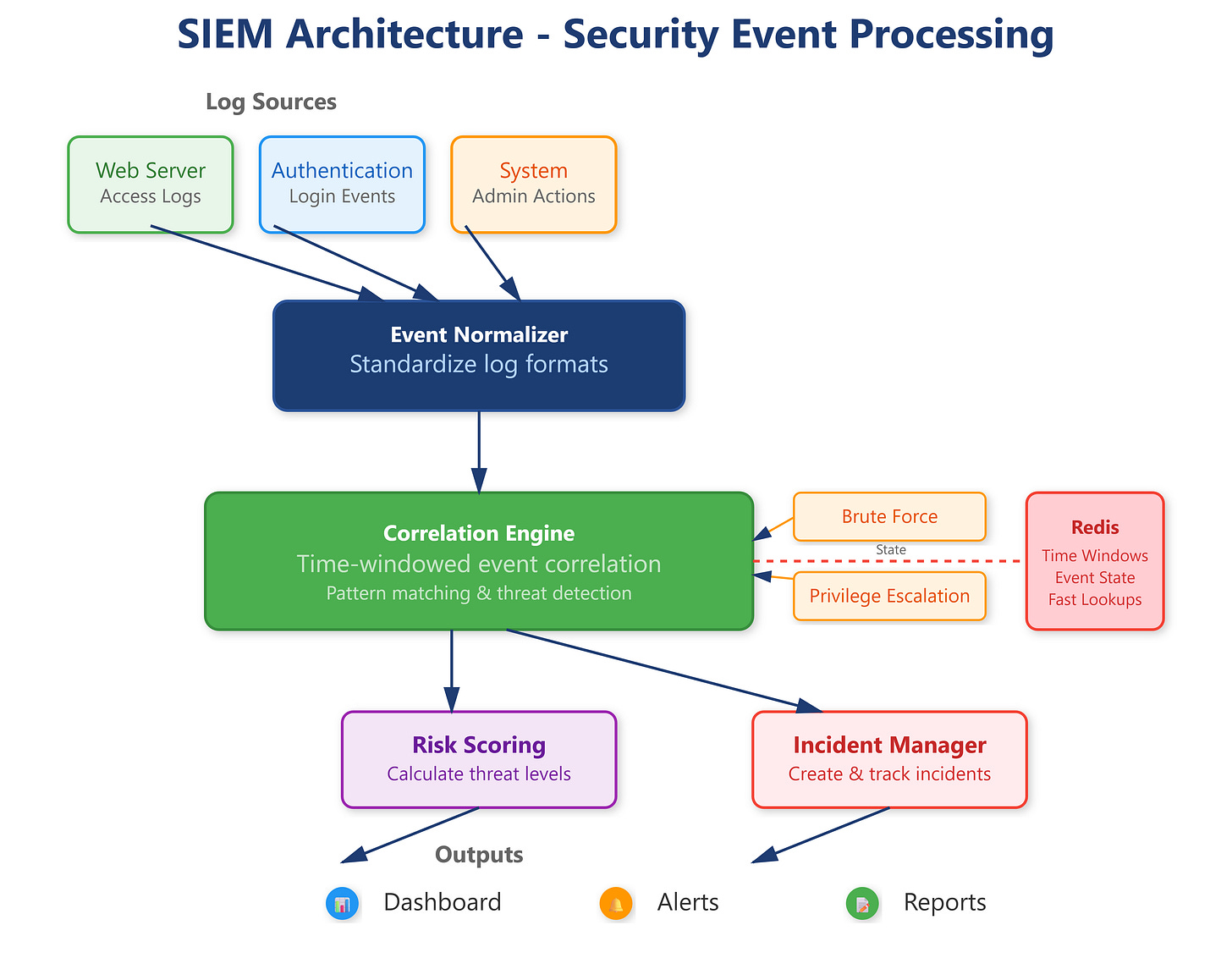
Today, you’re building a Security Information and Event Management (SIEM) system that transforms raw security logs into actionable intelligence. By lesson’s end, you’ll have a real-time security analytics platform that correlates events, detects anomalies, and alerts your team before attackers can cause damage.